Cyber attacks, supply chain attacks in particular, are growing in number by the day. Businesses are slow to react, at times unable to even. As a result, cybercriminals and threat actors have begun to target organizations of all sizes by hacking their accounts and blocking access to sensitive information until a ransom is paid, leading to losses worth millions of dollars. The recent high-profile ransomware attacks conducted on Colonial Pipeline and JBS have resulted in businesses getting a much-needed wake-up call to ramp up their cybersecurity.
Why are supply chain hacks getting more frequent?
In a supply chain network, a company produces goods that are distributed to various buyers via suppliers. Thus, through just one hack of the manufacturing company or third-party vendor, cybercriminals gain access to records and data of most, if not all, of the companies linked in the supply chain.
Cyber attackers usually target third-party vendors that have poor cybersecurity controls in place. The target is often a company with a large number of customers as these companies have delicate operations and will be forced to pay the ransom.
How Supply Chain Hacks Work
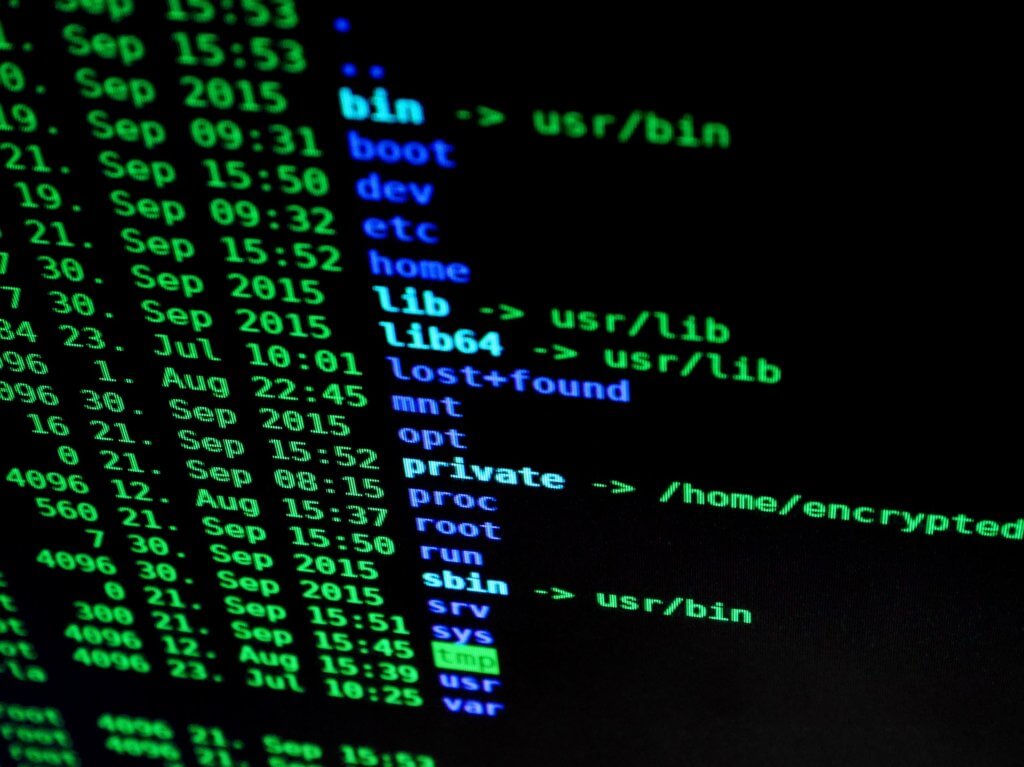
Supply chain attacks begin by breaching the security of the main company or a vendor. After that, other systems are hacked into using multiple attack vectors like viruses and malware, or even through subtle tactics like messages, email attachments, pop-ups, web pages, etc.
Once the attack vector is sent out, the malicious code embeds itself into the host’s digitally signed process and prevents detection by hiding behind the digital signature. This gives it the freedom to gain access to the network of the client and the compromised vendor via software updates.
Damages That Supply Chain Attacks Can Cause
The costs to any organization suffering from supply chain attacks can be enormous, not just through paying off the ransom but also through a loss of reputation, loss of business resulting from the breach, and even regulatory fees and fines.
It is estimated in the US that the average cost of a data breach was approximately $8.64 million. The healthcare sector was the most targeted, with data breaches amounting to $7.13 million on average, while the energy sector ($6.19 million) and finance sector ($5.56 million) also saw grave financial implications.
Biggest Supply Chain Attacks: 2020 and 2021
In March of 2020, SolarWinds fell victim to a supply chain attack, the biggest and costliest attack of the year. SolarWinds is a software developing company that sells software that monitors the networks of many businesses. Cyber attackers used malware that was sneaked into SolarWinds’ regular software update. Through that, attackers infiltrated and had access to the computer systems of top-secret US government agencies alongside 100 private companies.
In addition to the supply chain attacks of Colonial Pipeline and JBS in early 2021, Kaseya, an IT company, was also hacked into on the second of July. Kaseya provides IT solutions to multiple managed service providers (MSPs), due to which the attack saw around 1500 companies affected.
Should you be worried about your third-party vendors?
Businesses need to be more careful in dealing with third-party vendors who do not have effective cybersecurity policies in place. Vendors should be checked thoroughly for their cybersecurity practices as well as their reliability. Vendors at times need access to data such as records of customers and their information which can be obtained through attacks via software updates, application installers, and malware installed on connected devices.
How to Prevent a Supply Chain Attack
There is no surefire way to protect your business from a supply chain attack, as an attack can come from anywhere in various ways. What can be done, however, is ensure that the following security measures are in place to help minimize their effects:
- Choose suppliers who match your ideal cybersecurity standards.
- Ensure that vendors have cyber insurance.
- Request vendors to disclose how they utilize data such as customer details and place limitations where necessary.
- Ensure the security of IoT devices as they are vulnerable to cyber-attacks.
- Constantly amend and improve cybersecurity policies.

