150 different printers of HP were breached and caused securities issues.
Cyberbullying has been a hot topic since the beginning of the Internet. Many businesses didn’t take the hackers seriously until important data and information were compromised. But here’s the catch: companies still focus on main components like IT, servers, and emails. They secure these components and often forget that hacking is possible through minor items too. Printers are usually forgotten by IT personnel when it comes to securing them.
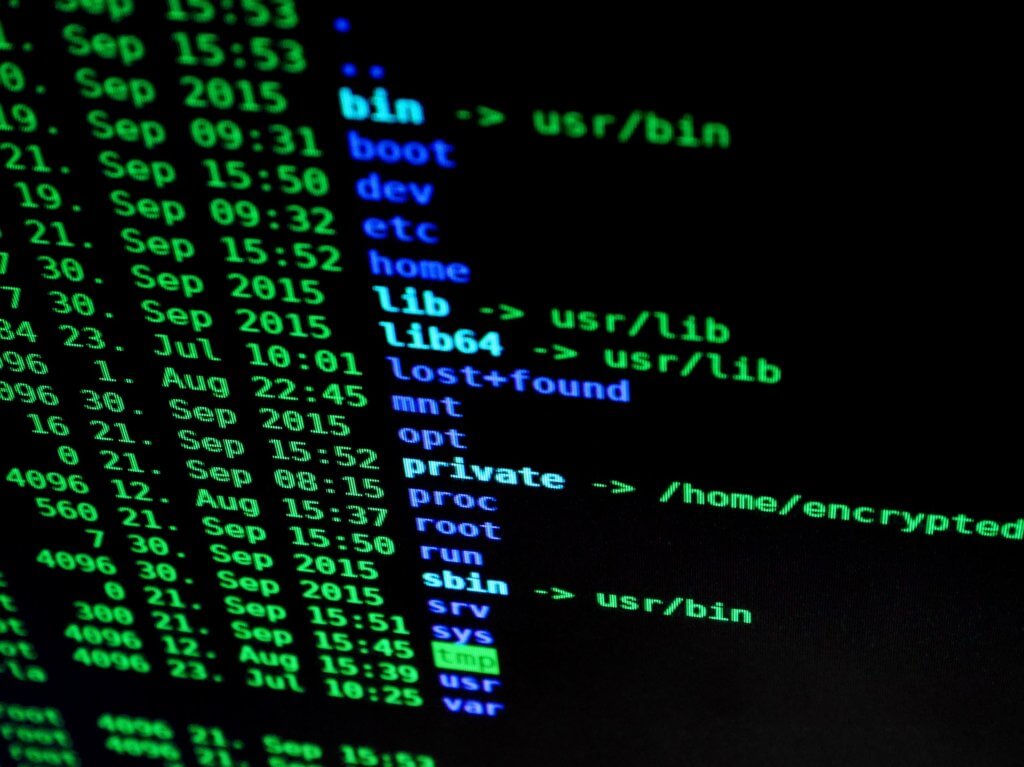
A security breach of more than 150 printers happened recently. The manufacturers of these printers were one of the biggest companies in the world: HP. Most of the important information a company possesses, like confidential documents and key data, go through a printer’s memory, and this could have done a lot of damage to the company’s reputation.
Tim Hirvonen and Alexander Bolshev, consultants of F-Secure Security, identified two different physical access vulnerabilities; port vulnerabilities (CVE-2021-39237) and font parsing vulnerabilities (CVE-2021-39238) in HP’s MFP (multi-function printer) M725z. Both of these vulnerabilities were identified in 150 HP printers.
How could malicious actors exploit these vulnerabilities?
Timo Hirvonen and Alexander Bolshev pin down several ways by which these vulnerabilities can be utilized by cybercriminals. Hackers would be able to destroy the business using these vulnerabilities through different methods. F-Secure Security consultants pinpoint a few ways that hackers could possibly use. The most common and dangerous way is to fool the organization into visiting a spiteful website. Another way could be exposing the company’s MFP and threatening them to do something suspicious.
The hackers could access any kind of secure information through printers, like having the ability to hack code execution rights. If the hacker has code execution rights, then he could access the customer’s and company’s confidential information as well.
Skilled hackers are the biggest threat
The consultants suggested that breaching this kind of information is not an easy task, but skilled cyberbullies can decode it with proper knowledge. Timo Hirvonen and Alexander Bolshev also said that the font parsing vulnerabilities could create a set of worms, which means that if the hacker could breach one printer through any sort of malware, it can spread automatically to other printers. So, tight security measures should be taken to keep the hacker at bay.
An important thing to remember is that the updated MFPs are fully automated, which means that they don’t require any kind of human interaction. Hackers find this kind of fully automated computer an opportunity as they are easy to corrupt.
Hackers are always updating themselves to the latest technology and finding ways to breach our security systems. If organizations don’t secure their MFPs like other endpoints, they are giving hackers an open invitation.
Fortunately, HP took the problem seriously as soon at it was realized, and made all the necessary measures to ensure the security of their printers.
The consultants recommended that companies should put their sensitive devices like printers in a secure place, and also make sure that no outsider has physical access to these devices.

